Dear Galaxy Finance,
Thank you for taking the time to look through our updated findings. Our mission and risk ratings are specifically based on hard-rug risk. This means that even if your project has good intentions, if the (usually anonymous and unknown) team can take out user funds, we mark the project as high-risk. This is a very simple rule but for ourselves and many among our community who have been rugged many times over before we learned about RugDoc, it has been highly profitable to take this rating into consideration. Of course it is not the only parameter that constitutes risk and should not be used in isolation. These other parameters also often determine whether we announce updates like this on Twitter and Telegram, something which we decided not to do in your case.
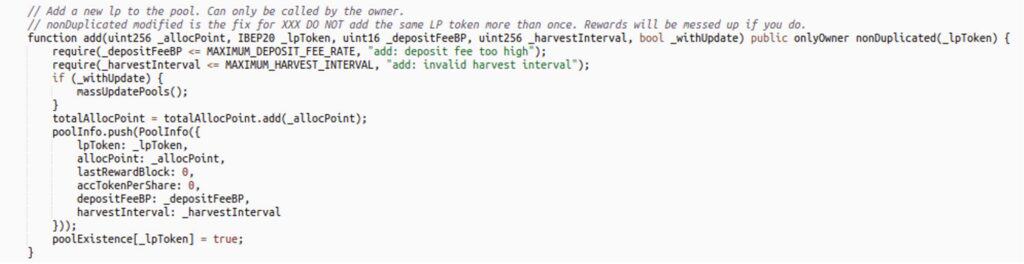
However, your project does have the exact hard-rug risk our whole mission is built around. First, notice the add function which allows you to add any LP pair as a pool. This could even be an LP pair consisting of two different LP pairs.
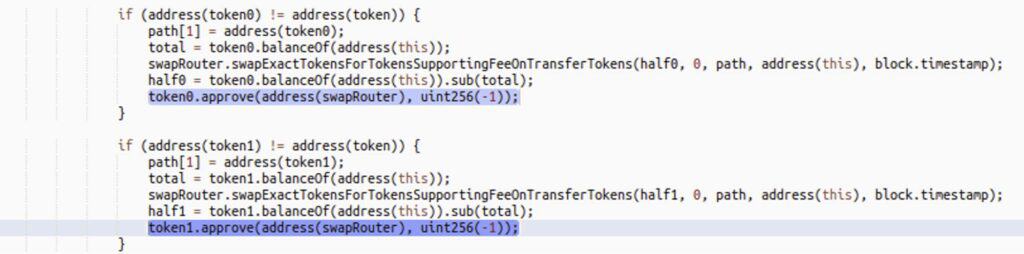
Now notice how during your compounding schedule, the router receives infinite approval to take out both tokens of the LP pair.
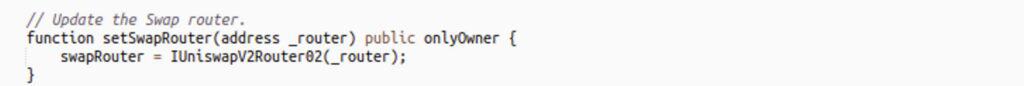
Given that your swap router can be upgraded to a malicious contract, this therefore allows a hard-rug of all staked funds.
Finally, let’s take a quick look at the weird emergencyWithdraw logic:
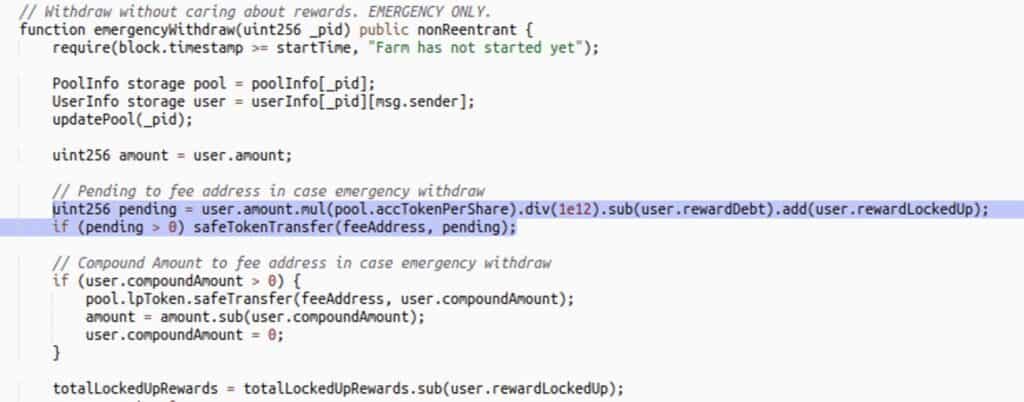
Here is a short list of some of the ways we found governance can prevent all withdrawals and emergency withdrawals. Once withdrawals are blocked, governance can just queue the rug transactions in the TimeLock.
- updateEmissionRate(type(uint256).max): UpdatePool or pending will revert due to overflow.
- safeTokenTransfer(feeAddress, pending): the operator of the TRITON token can include the MasterChef in anti-whale and set the anti-whale limit extremely low making this section always revert emergency withdrawals. Since the TRITON operator is an EOA, funds can be locked in at any moment and governance can take their sweet-sweet time to hard-rug all tokens.
- setFeeAddress(address newFeeAddress): The feeAddress on the token can be set to address(0) to revert all token transfers. This can be done instantly since the TRITON operator is an EOA (a wallet) and governance can again take their sweet-sweet time to hard-rug all tokens.
Emergency withdraw is a safe-haven for many investors. The function is so simple it almost never breaks unless there is hard-rug code. Making modifications like this that can result in all funds being locked is dangerous for user funds in case the project ever turns malicious and it is therefore in line with our mission to rate these changes as high-risk.
In case this is an honest mistake, you could consider moving to a safer version of the MasterChef, taking community safety into greater consideration.
To all users: As this open letter describes the project has the ability to lock in all funds at any point in time without having to go through TimeLock. Afterwards, the project can take as much time as they want to update the router to execute the hard-rug vector. The TimeLock is irrelevant. Although the project does look promising, this should be taken in consideration in your decision making process.